Peel Carefully
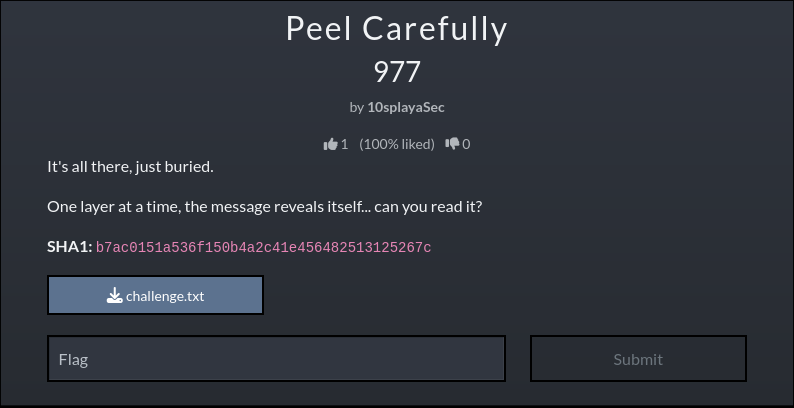
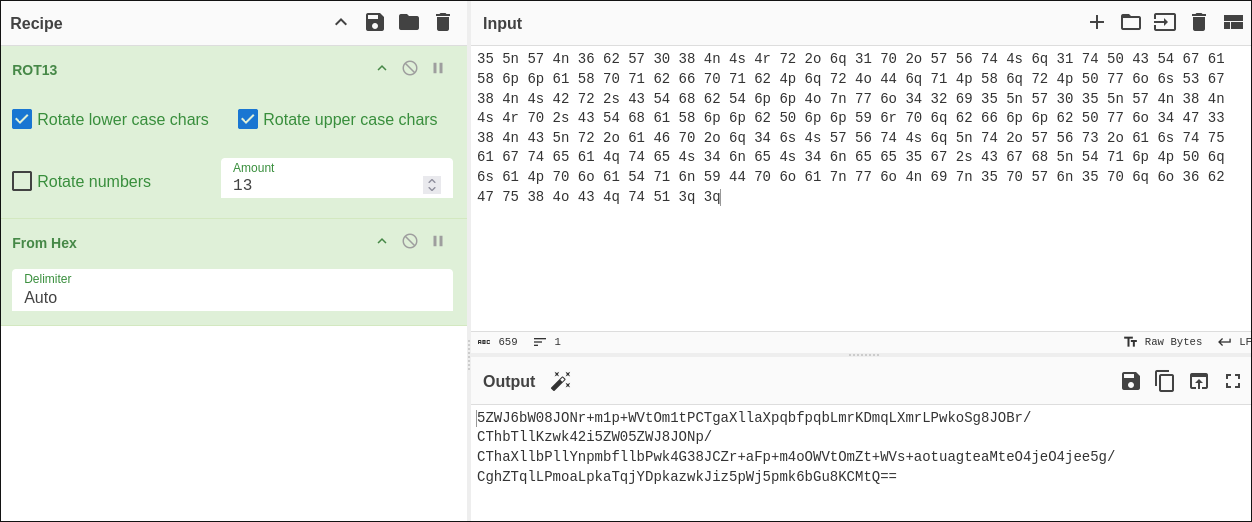
Description
Peel Carefully is a misc. problem from CTF@CIT 2026. Overall, it is a series of different encodings that you must systematically crack using different online tools.
Walk Through
After downloading the challenge.txt file and reading it, we can see that the file is full of dots and dashes.
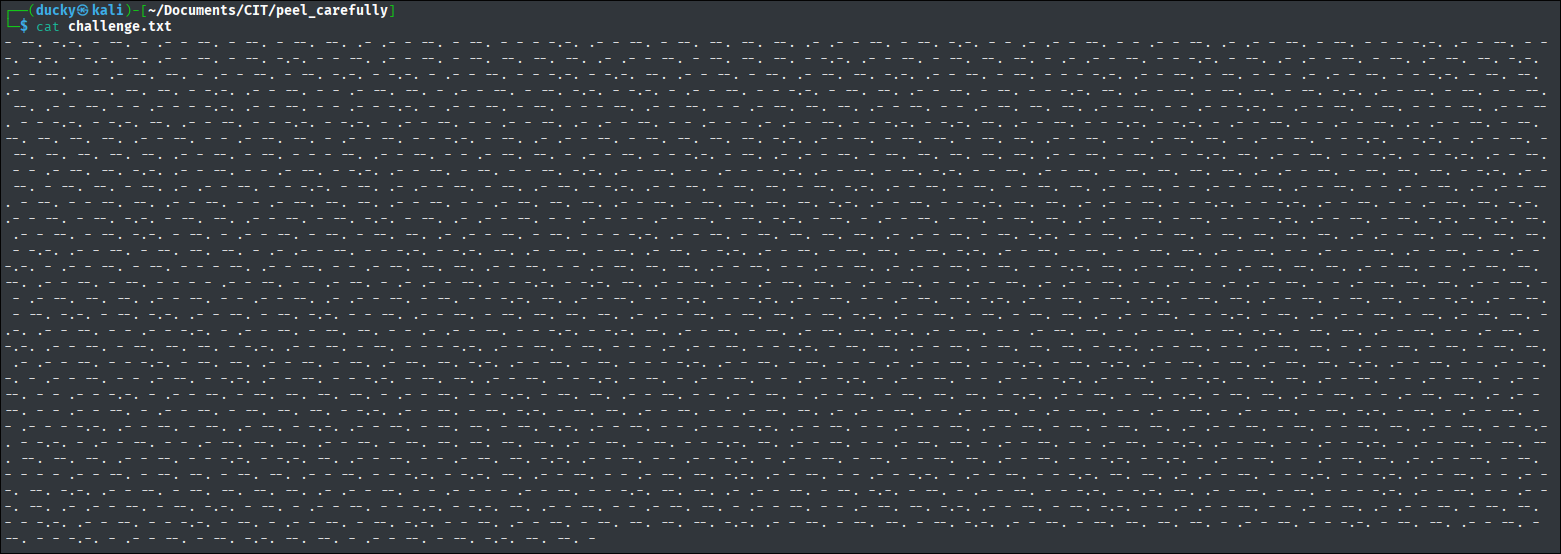
This looks exactly like Morse Code, so we need to find a tool to decode it.
The online tool Morse Code Translator works perfectly and outputs a series of letters. Specifically the letters A, C, G, and T.
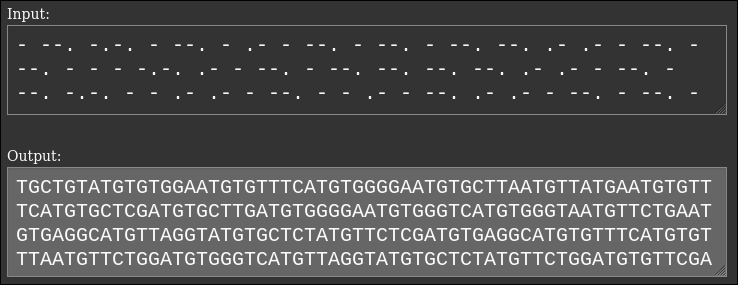
These letters represent a DNA sequence. The full sequence is shown below.
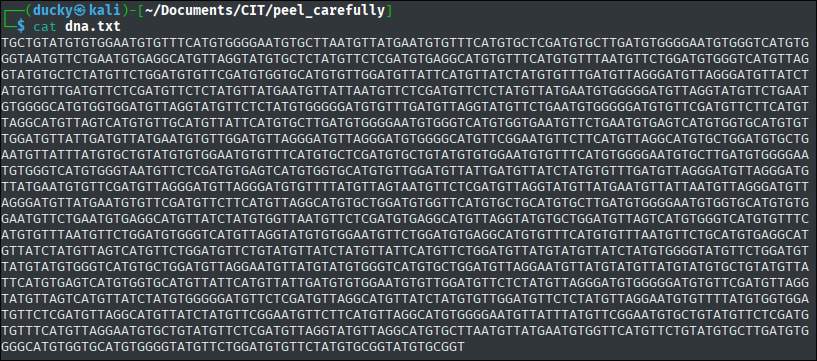
So what do we do with the DNA? My team and I explored a few different routes.
The first thing we tried was putting the sequence into the online tool Expasy to see if an amino acid sequence may have spit out a message. This got us nowhere.
Next, after a bit of research, we found DNA -> English and DNA -> Binary translation tables on John Hammond’s ctf katana GitHub repository. Both of these tables also lead nowhere.
Finally, we found an online tool, Cache Sleuth,1 that decodes DNA sequences into a-z, A-Z, and 0-9. Actually decoding the DNA using this tool gives us a hex byte looking sequence. These are not really hex bytes, but they are very close.
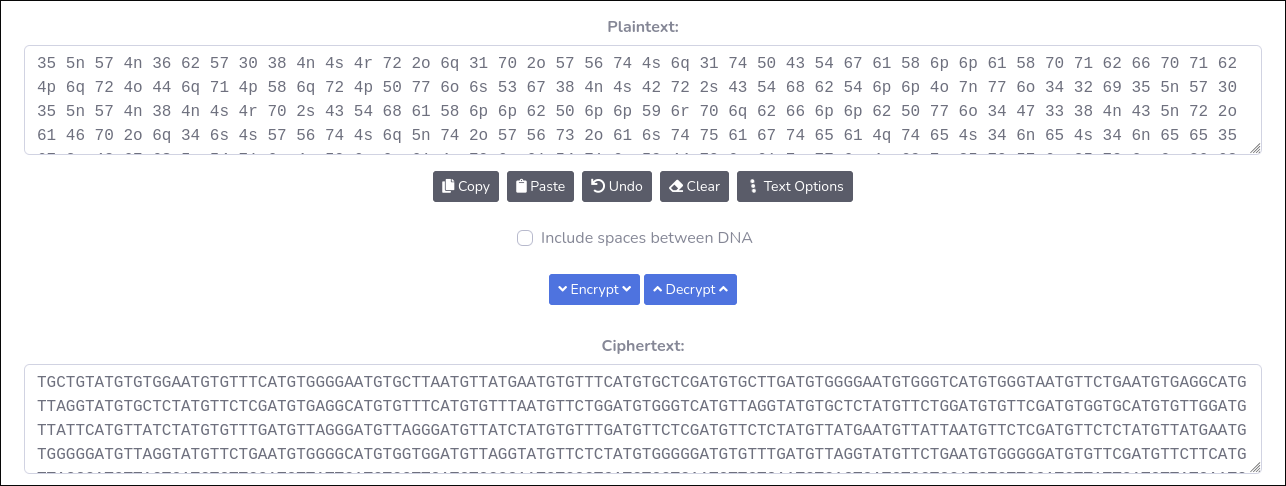
The full output of the almost hex bytes is shown below.
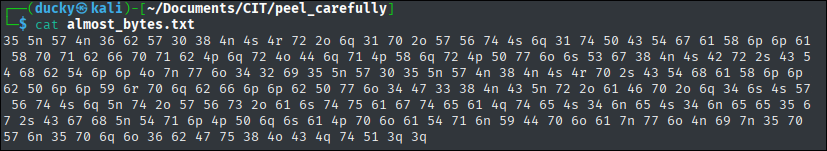
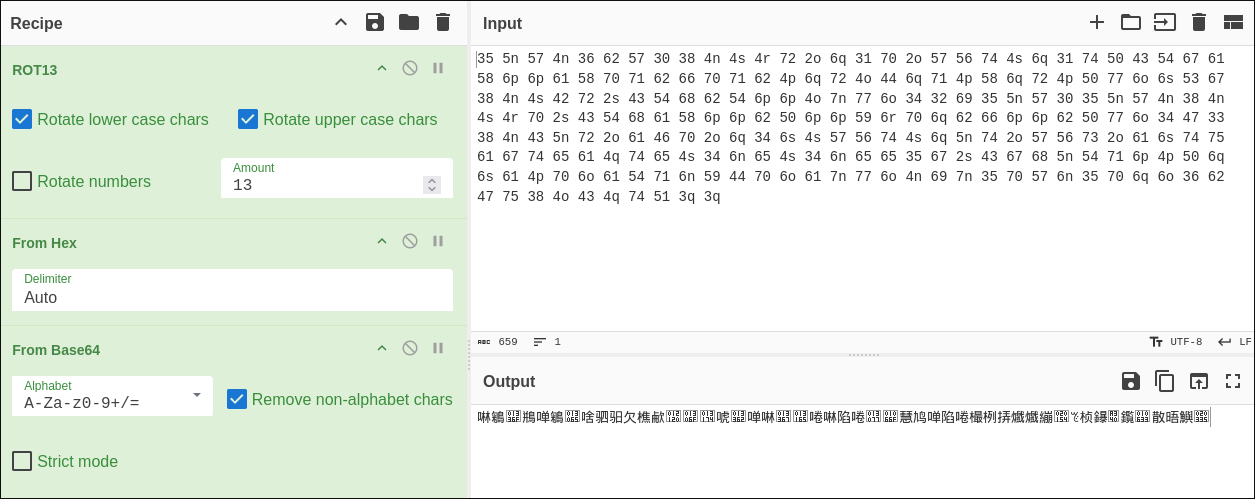
So, we need to make these almost bytes into actual bytes. Sounds like a job for everyone’s favorite cipher swiss army knife, CyberChef. After putting the almost bytes into CyberChef and preforming a rot13, we have actual hex bytes.
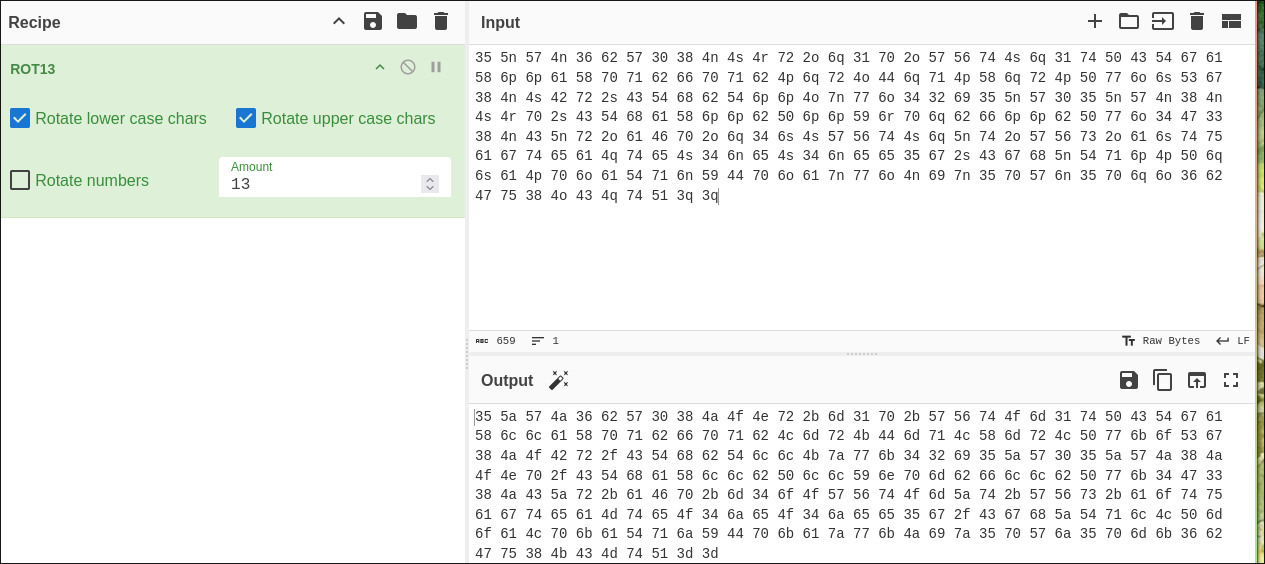
Furthermore, after preforming the From Hex operation, we get a Base64 string.
Using the From Base64 operation gives us some very interesting characters.
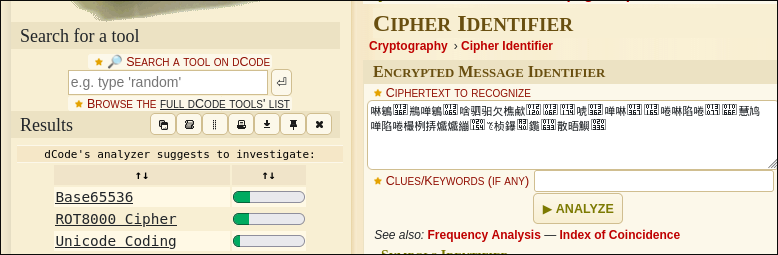
To figure out what to do next, we used the cipher identifier on dcode. This told us that we were likely working with a Base65536 encoding.
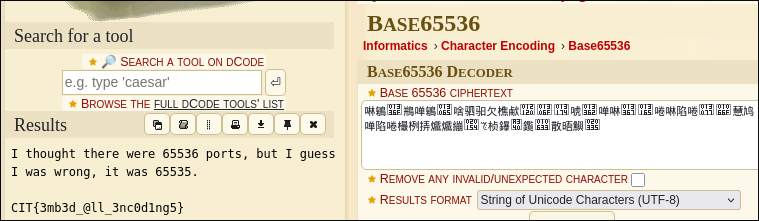
We can use dcode again to actually decode the Base65536 string and get the flag.
Reflection
This was a very interesting challenge, and as the name and challenge description suggested there were many layers to peel back. I have never seen DNA used for flag encoding purposes before, so having to explore different avenues to find the correct path forward was a bit of a challenge. This was also my first time using the cipher identifier tool in dcode, and I will definitely continue to use it in the future.